DAST and SAST: Key Differences & How to Choose the Best Security Tools
When you boil it down, the difference between SAST and DAST is pretty straightforward. Think of it like this: SAST inspects a building's blueprints for design flaws, while DAST stress-tests the finished building to find structural weaknesses.
One looks at your application's source code from the inside before it ever runs (SAST), and the other pokes and prods the live, running application from the outside (DAST). Both are absolutely critical, but they come at the problem from completely different angles and at different times.
Understanding DAST and SAST Methodologies

To really get a handle on DAST and SAST, you have to look at how they work under the hood. They aren't competing tools you choose between; they’re two complementary pieces of a solid security strategy. Each gives you a unique window into your application's weak spots.
The White-Box Approach of SAST
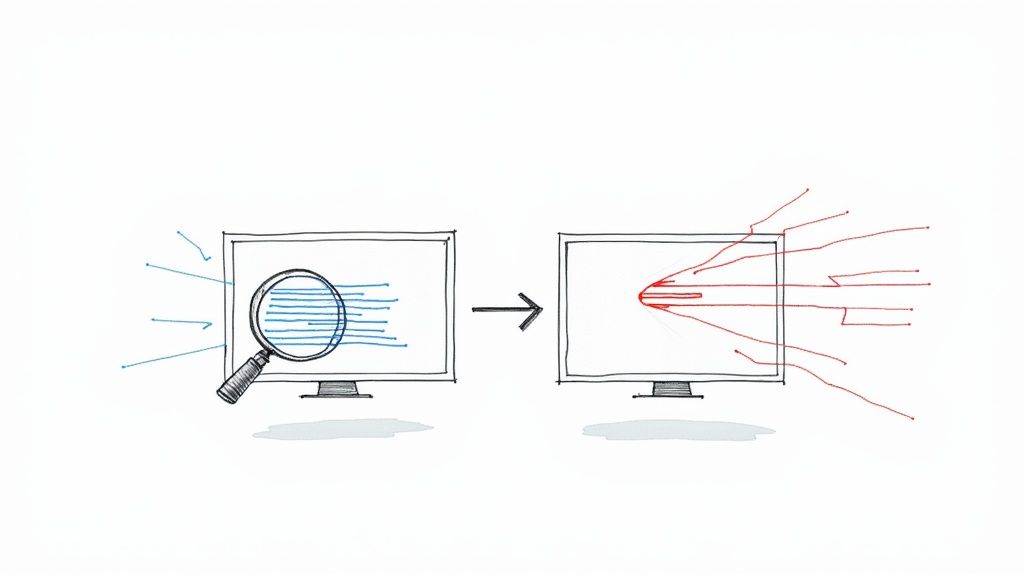
SAST is what we call a white-box testing method. That means it gets full, unrestricted access to the application's internal wiring—the source code itself. It acts like a tireless, automated code reviewer, meticulously scanning every line of your source code, bytecode, or binaries for known vulnerability patterns. It does all of this without ever executing the program.
This inside-out view is its superpower. It allows SAST to spot issues incredibly early in the Software Development Lifecycle (SDLC), sometimes right inside a developer's IDE. It’s fantastic at sniffing out specific coding mistakes like SQL injection vulnerabilities, buffer overflows, and other insecure practices that could easily be missed until it’s too late.
The Black-Box Approach of DAST
On the flip side, DAST takes a black-box testing approach. It knows absolutely nothing about the source code or the application's architecture. Instead, it behaves just like a real user—or, more accurately, an attacker—would. It throws all sorts of inputs at the running application and carefully watches the responses to see if it can break something or expose a security hole.
This perspective is invaluable for catching runtime vulnerabilities that static analysis just can't see. We're talking about things like server misconfigurations, broken authentication, session management flaws, and many cross-site scripting (XSS) issues that only pop up when all the application's components are assembled and running together.
Key Takeaway: Think of it this way: SAST checks the ingredients and the recipe for potential problems before you start cooking. DAST, on the other hand, tastes the finished meal to see if anything went wrong during the cooking process.
This quick comparison really drives home their distinct roles:
| Attribute | SAST (Static Testing) | DAST (Dynamic Testing) |
|---|---|---|
| Testing Approach | White-box (analyzes source code) | Black-box (tests running application) |
| When to Use | Early in the SDLC (coding, commit) | Later in the SDLC (testing, staging) |
| Code Access | Requires access to source code | No source code access needed |
| Vulnerability Types | Finds coding flaws (SQL injection) | Finds runtime issues (misconfigurations) |
| Environment | Language-dependent | Language-agnostic |
How SAST Finds Vulnerabilities in Your Codebase
Think of Static Application Security Testing (SAST) as an expert code reviewer that works tirelessly and automatically. It meticulously inspects your application's source code, bytecode, or binaries without ever actually running the program. This "white-box" method gives it full visibility into your software's internal structure, letting it spot potential security weaknesses right at their source.
Unlike dynamic testing that watches for weird behavior, SAST is all about structure and patterns. It creates a model of your application's architecture, tracing the control flow (how the program runs) and the data flow (how information moves around). This deep dive helps uncover vulnerabilities that could otherwise stay buried until an attacker finds them.
Pinpointing Flaws with Code-Level Precision
SAST tools are trained to spot the tell-tale signs of common vulnerabilities. They check your code against a massive database of known insecure coding practices, flagging the specific lines or blocks that create a security risk. This makes them incredibly effective at catching certain kinds of issues.
Common vulnerabilities that SAST is great at detecting include:
- SQL Injection: It finds where user input isn't properly cleaned before being sent to a database query, shutting down a classic and dangerous attack.
- Buffer Overflows: SAST can spot code that lets data get written outside of its assigned memory space—a flaw that can cause crashes or even allow arbitrary code execution.
- Cross-Site Scripting (XSS) Flaws: It highlights spots where untrusted input is sent back to a user without proper encoding, which could let attackers inject malicious scripts.
- Insecure Deserialization: The tool can flag the unsafe handling of serialized data objects, which attackers could manipulate to execute remote code.
By analyzing code before it's ever compiled or run, SAST finds the root cause of a vulnerability, not just a symptom. This lets developers fix the problem exactly where it starts, making the fix permanent and truly effective.
This level of detail is a massive advantage. Instead of just flagging that a vulnerability exists, a SAST tool can often point to the exact file and line number, which dramatically speeds up the debugging process. You can get a deeper technical look into this by exploring our guide on what is static analysis.
The Power of Shifting Left
The single biggest win with SAST is its ability to "shift left"—embedding security testing into the very beginning of the software development lifecycle (SDLC). Since it doesn't need a running application, you can run scans directly inside a developer's IDE or as an automated step in your CI/CD pipeline every time code is committed.
This early detection turns security from a last-minute headache into an ongoing part of the development workflow. Studies have shown that fixing a bug in production can be up to 100 times more expensive than fixing it during development. SAST hits this problem head-on by giving developers instant feedback while the code is still fresh in their minds.
But SAST isn't a silver bullet. Its greatest strength—the deep code analysis—is also the source of its main drawback: the potential for false positives. Because the tool doesn't understand the full runtime context, it might flag theoretical issues that aren't actually exploitable in the live app. Fine-tuning the tool and managing these alerts is key.
Plus, it can't find runtime or environment-specific problems like server misconfigurations or authentication flaws. That’s where DAST comes in to complete the picture.
Simulating Real-World Attacks with DAST
While SAST inspects the blueprints, Dynamic Application Security Testing (DAST) stress-tests the finished structure. It operates from the outside-in, behaving like an automated ethical hacker to find vulnerabilities that only appear when an application is actually running. This "black-box" perspective is essential for a complete security posture.
DAST tools interact with your application without any knowledge of its internal source code or architecture. They probe it with a barrage of simulated attacks—sending malicious payloads, manipulating HTTP requests, and trying to bypass security controls. This is crucial for identifying how different components interact and where runtime weaknesses might exist.
Uncovering Runtime Vulnerabilities
The real power of DAST is its ability to find security flaws that are completely invisible to static analysis. Because it tests the live application, it can discover entire classes of vulnerabilities that SAST tools simply cannot see.
A DAST scan is great at identifying issues like:
- Server Misconfigurations: Exposing sensitive information or services due to an improper server setup.
- Authentication and Session Management Flaws: Allowing attackers to impersonate users or hijack active sessions.
- Runtime-Specific Injection Flaws: Finding vulnerabilities like Cross-Site Scripting (XSS) that depend entirely on how the application processes and renders user input in real-time.
This focus on the live environment makes DAST language-agnostic. It doesn't care if your application is written in Python, Java, or a mix of languages; as long as it communicates over HTTP/S, DAST can test it. That makes it exceptionally versatile for modern, complex architectures.
The growing need for this kind of runtime analysis is obvious in the market trends. The Dynamic Application Security Testing market is projected to expand significantly, reaching an estimated $8.52 billion by 2030. This growth is fueled by the rising frequency of web application attacks and stricter regulatory demands worldwide. You can discover more insights about DAST market trends to see how the industry is evolving.
The Tradeoffs of a Black-Box Approach
For all its power, DAST has inherent limitations tied to its black-box nature. Since it interacts with the application from the outside, it can't pinpoint the exact line of vulnerable code. Instead of reporting "vulnerability in file X at line Y," it will tell you that a specific endpoint or feature is vulnerable.
This means that while DAST is excellent at confirming a vulnerability is real and exploitable, the fix requires more legwork from developers to trace the symptom back to its root cause in the code.
Another key consideration is timing. DAST scans can only happen later in the Software Development Lifecycle (SDLC) once there’s a running application to test, typically in a staging or QA environment. This is a sharp contrast to the "shift-left" ideal of SAST, which finds flaws much earlier. Integrating DAST effectively requires careful planning to avoid creating bottlenecks right before a production release.
Let's look at a practical scenario. Imagine a developer writes code that properly sanitizes user input, which easily passes a SAST scan. However, a misconfiguration on the production web server disables a crucial security header. SAST would never see this, but a DAST scan would immediately flag the misconfiguration as a high-risk vulnerability. This example perfectly shows why you need both DAST and SAST for comprehensive coverage.
A Side-by-Side Comparison of SAST and DAST
To make the right security decisions, you have to go beyond the basic definitions and look at how Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) stack up where it really counts. While both are designed to secure your software, they couldn't be more different in their methods, timing, and the kind of feedback they give you. Understanding these nuances is the key to building a security strategy that actually works.
The fundamental difference comes down to perspective. SAST takes a "white-box" view, digging into your application's source code from the inside out before it ever runs. On the flip side, DAST uses a "black-box" approach, poking and prodding the running application just like an attacker would, without any knowledge of the code underneath.
This visual gives a quick breakdown of how they differ in detection, coverage, and even their typical false positive rates.
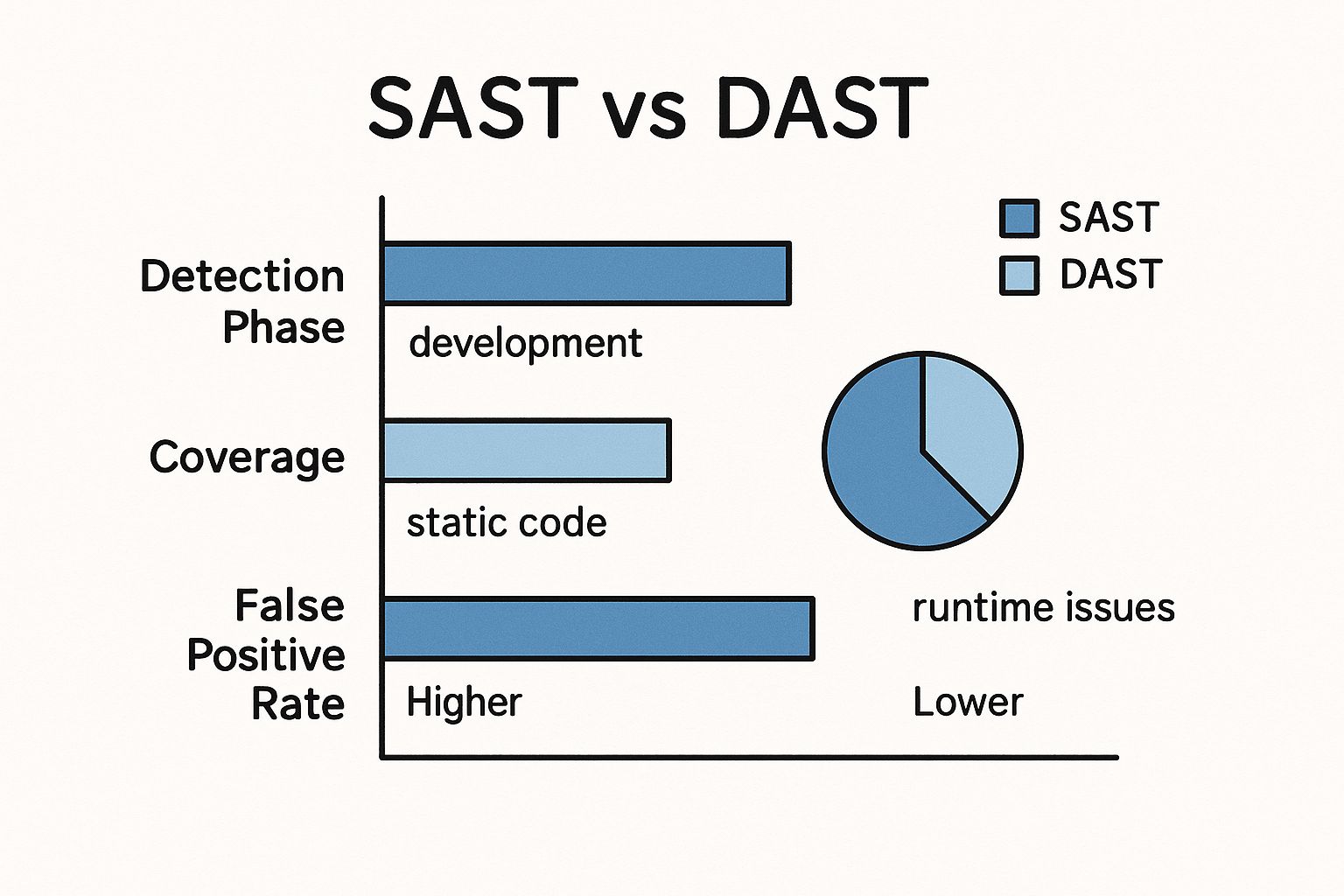
As you can see, SAST gets to work early in development, sniffing out static code issues. DAST, however, comes in later to find runtime vulnerabilities once the application is up and running in a real-world environment.
Core Methodology and Timing
The biggest split between DAST and SAST is how and when they test. SAST analyzes static code, which means it can be baked right into the earliest stages of the Software Development Lifecycle (SDLC). We're talking directly in a developer's IDE or as part of a commit hook. This "shift-left" strategy catches vulnerabilities before the code is even compiled.
DAST, however, needs a running application to do its job. This places it much later in the SDLC—typically during QA, staging, or even in production. It simulates real attacks against live endpoints, giving you a brutally honest assessment of how your application would hold up against a real threat.
Vulnerability Coverage and Scope
Each tool is built to find a different class of security flaws, which is why they work so well together. They aren't competitors; they're complementary.
- SAST is king at finding: Implementation-level bugs hiding in the source code. Think classic issues like SQL injection, buffer overflows, and insecure coding patterns that a smart tool can spot by analyzing data and control flows.
- DAST shines at finding: Runtime and environment-specific problems that are invisible to a code scanner. This includes server misconfigurations, authentication bypasses, and session management flaws that only show up when the application is live.
The crucial takeaway is this: SAST secures the code, while DAST secures the running application. One finds flaws in the architectural blueprint; the other finds weaknesses in the finished building. You need both.
Both SAST and DAST have become essential in modern software security, especially as DevOps and Agile have taken over. One looks at source code without running it, the other tests the live application—they're targeting vulnerabilities from two completely different angles. You can discover more insights about application security with SAST and DAST to see how they fit into today's fast-paced workflows.
Feedback and Remediation
The feedback you get from each tool is a direct reflection of its approach. A SAST tool can point to the exact file and line number where a vulnerability lives. For a developer, that’s gold—it makes navigating to the problem and fixing it incredibly straightforward.
DAST, in contrast, reports vulnerabilities based on endpoints and application behavior. It might tell you a specific API endpoint is vulnerable to cross-site scripting, but it has no idea which lines of code are to blame. This leaves developers with the task of playing detective, tracing the symptom back to its root cause in the codebase, which can definitely take more time.
To make things even clearer, let's break down the key differentiators in a simple table.
Key Differentiators: SAST vs. DAST
This table provides a detailed breakdown comparing SAST and DAST across the most important attributes in the application security testing process.
| Attribute | SAST (Static Testing) | DAST (Dynamic Testing) |
|---|---|---|
| Testing Approach | White-Box: Analyzes internal source code and structure. | Black-Box: Tests the external behavior of a running application. |
| SDLC Stage | Early: Coding, committing, and building phases. | Late: Testing, staging, and post-deployment phases. |
| Typical Findings | Coding errors, SQL injection, buffer overflows. | Server misconfigurations, authentication flaws, runtime errors. |
| Remediation | Provides exact file and line number for fast fixes. | Reports vulnerable endpoints, requiring investigation. |
| False Positives | Can be higher, as it lacks runtime context. | Generally lower, as it confirms exploitable vulnerabilities. |
Ultimately, choosing between them isn't the right way to think about it. The real question is how to layer them effectively to cover all your bases, from the first line of code written to the final application running in production.
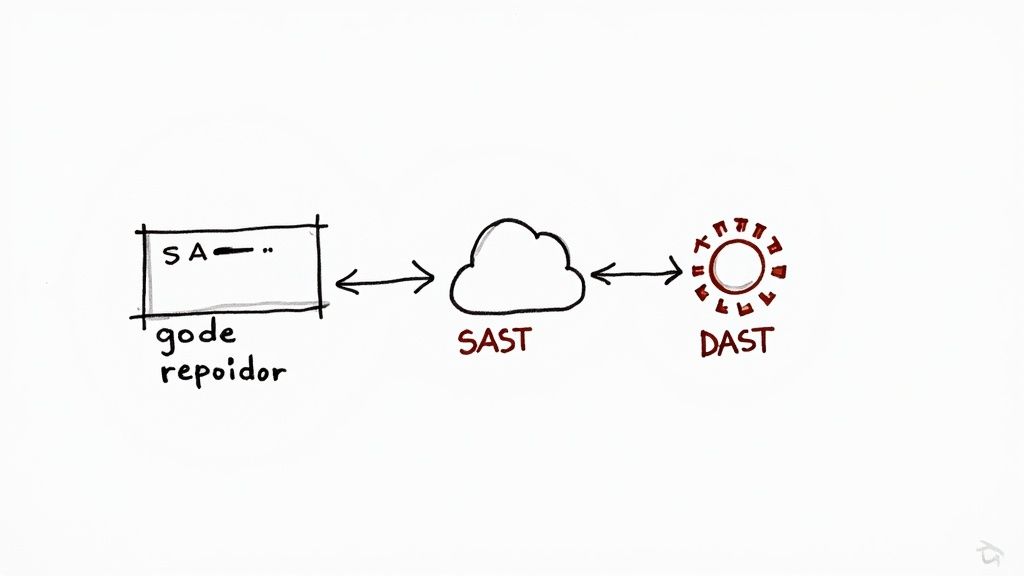
Integrating DAST and SAST into Your CI/CD Pipeline
So, you have the tools. Great. But just owning DAST and SAST scanners isn't enough—the real magic happens when you weave them thoughtfully into your CI/CD pipeline. The goal is to build a DevSecOps workflow where security isn’t a final, painful gate blocking a release, but an automated, continuous part of the development rhythm.
When you embed both static and dynamic testing into your pipeline, you create layers of defense. This approach turns security from a periodic audit into a real-time feedback loop, catching vulnerabilities earlier, cutting the cost of fixing them, and building a much stronger security culture on your team.
Shifting Left with SAST Integration
"Shifting left" is all about finding and squashing security bugs as early as humanly possible. SAST is your best friend here because it works directly on the source code, long before there's a running application to test. To make it work, you have to put SAST scans right where your developers live and breathe.
Here’s where to plug SAST in:
- In the Developer's IDE: Most modern SAST tools offer plugins for editors like VS Code or IntelliJ. This gives developers instant feedback, flagging issues as they type. It’s the cheapest and fastest way to fix a problem—before it even becomes a problem.
- With Pre-Commit Hooks: You can set up Git hooks to run a lightning-fast SAST scan on changed files before a developer can even commit their code. Think of it as a first line of defense against obvious mistakes.
- On Every Pull Request: This is the big one. Automating a SAST scan for every single pull request is non-negotiable. It guarantees that no new code gets merged into your main branch without a security checkup. The results pop up right in the PR, making security a natural part of the code review conversation.
By automating these checks, you empower developers to own the security of their code. The feedback is immediate and right in context, which feels collaborative, not confrontational.
Key Insight: Integrating SAST into pull requests transforms security from a bottleneck into a conversation. It allows teams to discuss, prioritize, and fix vulnerabilities as part of the standard code review process, making security a shared responsibility.
Automating DAST in Later Stages
While SAST has your code covered, DAST is there to protect the running application. It naturally fits later in the CI/CD pipeline, after your code has been built and pushed to a test environment. This is where you’ll catch all the runtime issues that SAST, by its very nature, can't see.
Automating DAST is critical to keeping your development velocity up. A typical workflow looks something like this:
- Trigger on Deployment: Your CI/CD pipeline automatically deploys the latest build to a staging or QA environment.
- Kick Off the DAST Scan: As soon as the deployment is live, a hook tells your DAST tool to start scanning the application at its URL.
- Analyze and Report Back: The DAST tool goes to work, simulating real-world attacks and reporting what it finds. You can even configure it to "break the build" if it uncovers high-severity vulnerabilities, stopping a bad release in its tracks.
- Close the Feedback Loop: The results are then pushed into ticketing systems like Jira, creating clear, actionable tasks for the development team to tackle in the next sprint.
This automated cycle ensures every build gets battle-tested against realistic attack vectors before it gets anywhere close to production. For a deeper look into the pipeline's role, you can learn why CI/CD is important in a DevOps lifecycle and see how security is a core piece of this automated world.
Best Practices for a Smooth Integration
Just plugging in DAST and SAST tools isn't the finish line. Without a smart strategy, you’ll drown your team in alerts. Security tools can easily create more noise than signal, leading to "alert fatigue" where even the important findings get ignored.
Here are a few practices that will save you a lot of headaches:
- Tune for a Low False Positive Rate: Spend real time configuring your SAST rules to match your codebase and frameworks. Disable irrelevant checks and fine-tune sensitivities to cut down on the false alarms that waste everyone's time.
- Start Small, Then Iterate: Don't flip every switch on day one. Begin by scanning for a handful of high-impact vulnerabilities, like SQL injection, and then gradually expand your rule set as the team gets comfortable with the flow.
- Automate the Triage Process: Use policies to automatically classify and prioritize what you find. For example, a critical vulnerability in a PR might automatically fail the build, while a minor issue just creates a low-priority ticket.
- Don't Break the Build Recklessly: Be strategic about what stops a deployment. Only the most severe, high-confidence findings should be build-breakers. Being too aggressive just creates frustration and tempts developers to find ways around the security checks.
Choosing the Right Strategy: SAST, DAST, or Both?
The real question isn’t about picking a side in the SAST vs. DAST debate. It’s about understanding which tool to grab for the job at hand and, more importantly, when to use them together for a layered defense. A one-size-fits-all approach to security just doesn't cut it. Your decision should always come down to your application's architecture, your team's maturity, and your specific risk profile.
For instance, if you're staring down a legacy codebase with years of technical debt and spotty test coverage, SAST is your most practical first step. It lets you scan the entire repository and catalog those deep-seated coding flaws before you even think about spinning up a test environment.
Scenario-Based Decision Making
On the flip side, a modern, public-facing API handling sensitive user data demands rigorous DAST from day one. In this situation, runtime vulnerabilities like authentication bypasses or sneaky server misconfigurations pose a much more immediate and severe threat. SAST alone would be completely blind to these critical, real-world attack vectors.
Let's break down a few common scenarios to help guide your strategy:
- For internal-facing applications with a lower external threat profile, a solid SAST program baked into the CI/CD pipeline often provides enough coverage to start.
- For applications subject to strict regulatory compliance like PCI DSS or HIPAA, using both DAST and SAST is pretty much non-negotiable. These standards demand comprehensive testing that covers flaws from the code level all the way to runtime.
- For fast-moving startups focused on shipping quickly, integrating a lightweight SAST tool into pull requests is a huge win. It catches common mistakes right away without slowing developers down. DAST can be layered in as the product matures.
The growing emphasis on runtime security is clearly reflected in market trends. In 2024, North America's DAST market was valued at USD 0.58 billion and is projected to hit USD 2.11 billion by 2033. This growth is fueled by regulatory demands and the simple, critical need to secure live applications.
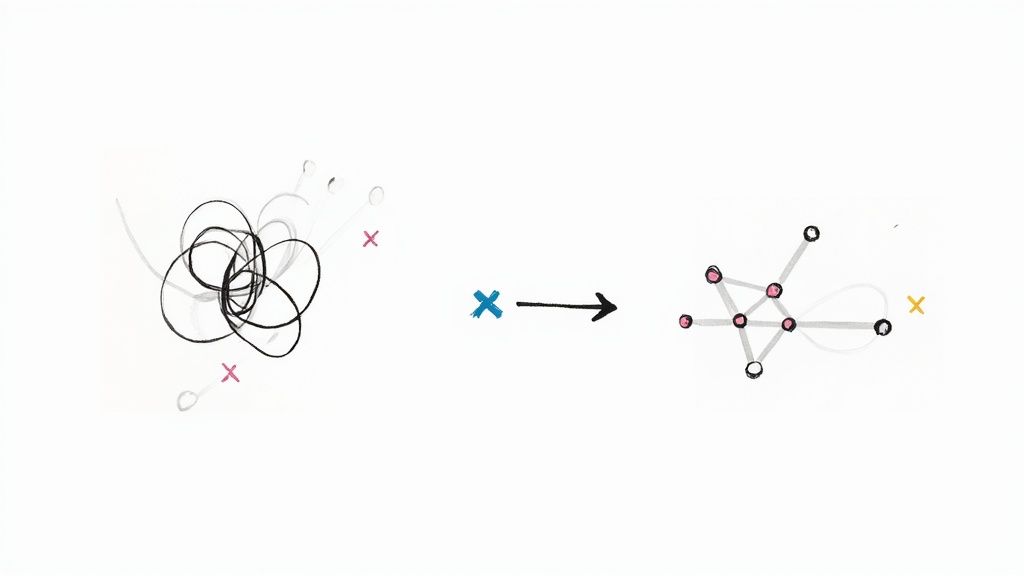
Adopting a Defense-in-Depth Model
Ultimately, a mature security program doesn't choose between SAST and DAST—it uses both. This combination creates a powerful defense-in-depth strategy that protects your application from the inside out and the outside in. SAST secures the code before it ever gets deployed, while DAST validates the security of the final, running product.
The most effective approach layers SAST and DAST to create a security net with no gaps. Think of it this way: SAST finds the flaws in the blueprint, while DAST stress-tests the finished building to make sure it's secure from every angle.
When you're evaluating DAST and SAST tools, it's crucial to think about how they fit into your overall software quality assurance processes. These tools are just one piece of a much broader strategy that should also include manual code reviews, penetration testing, and secure development training.
By integrating both tools into your automated workflows, you create a continuous feedback loop that makes security a shared responsibility. Finding the right balance will depend on your organization's specific needs, but the goal is always the same: build and ship secure software without killing your momentum. You can also explore a detailed CI/CD tools comparison to see how different platforms can support this integrated approach.
Common Questions About DAST and SAST
As development teams get serious about security testing, a few key questions about DAST and SAST always seem to pop up. Getting these answers right is the difference between a security process that works and one that just adds friction to your workflow.
Let's clear up some of the most common points of confusion.
Can One Tool Replace the Other?
The short answer is no. This is one of the most common misconceptions out there. SAST and DAST aren't competitors; they're partners in a good security strategy.
Think of it this way: SAST is like inspecting the blueprints of a building for design flaws. It checks your code from the inside out before anything is even built. DAST, on the other hand, is like hiring an inspector to test the finished building—checking the locks, rattling the windows, and making sure it's secure from the outside.
If you only use one, you're leaving massive blind spots. A perfect SAST scan won't tell you about a misconfigured server, and a clean DAST scan can’t spot a deeply buried flaw in your code that an attacker might find later. A mature security posture needs both for true defense-in-depth.
How Do They Handle Modern Architectures?
This is where things get interesting. Modern applications, especially those running on microservices or as Single-Page Applications (SPAs), throw a wrench in the works for older testing tools.
- SAST tools can get lost in the disconnected world of microservices. They often lack the full context to understand how different services interact, which can lead to missed vulnerabilities or false positives.
- DAST tools need to be smart enough to navigate the complex, JavaScript-heavy world of SPAs and properly test the APIs that connect all the different pieces.
The good news is that modern security tools are adapting. Top-tier tools now come with much better API scanning capabilities and features designed to trace interactions between services.
A third approach, Interactive Application Security Testing (IAST), is also gaining traction. IAST instruments the running application, giving it the code-level view of SAST combined with the real-world execution context of DAST. It’s a powerful hybrid solution for complex apps.
Ultimately, picking the right tool means making sure it understands your tech stack. You need accurate, actionable feedback that fits how you actually build software today.
Ready to secure your CI/CD pipeline and eliminate merge conflicts? Mergify provides the tools you need to automate your workflow, reduce CI costs, and ship code faster and more securely. Discover how Mergify can transform your development process.